This Domino’s phishing email is a real ‘pizza work’

At half 1 on a Thursday afternoon, having worked my way through a pile of documents, this humble Mirus employee felt a violent rumbling in their stomach. I’d skipped an early lunch to get through a huge pile of outstanding work, and right about then, a deep crust Americano (double pepperoni) would have gone down an absolute treat.
Somewhere, on the other side of the internet, a virtuous pizzaiolo overheard this siren call. “Golly!”, he proclaimed, eager to attend to this writer’s wailing stomach. “I’d better make this famished wastrel aware of the fantastic offers available from Domino’s Pizza – that’ll sort the poor blighter right out!”.
And with that, said pizzaiolo sent a highly convincing, mouth-watering and entirely fake email over to your starving writer. Yep – this was a fraud email, and I’m sure whoever sent it was cooking up something much more malicious than a simple pizza.
I must hand it to fraudster; this email drips authenticity like a Meat Feast drips saturated fats. The branding’s unmistakeable, the offers are reasonable, and they even have the cheek to warn me of fraudsters, right down there in the smaller print.
Somebody’s done their research too – there, at the top of the email, is my own first name. Had I not known any better, I’d have clicked on one of these tantalising offers and expected a piping-hot pie within minutes.
Fortunately, I did know better, and I lumped this email right in the Spam folder. Here’s why:
I wasn’t expecting an email from Domino’s
Now, don’t get me wrong: I’ve ordered plenty of Domino’s in my time (more than I’d like to admit, frankly), but not once have I ever ordered a Domino’s from my work email. Not only is it a breach of our email policy, but I’d be forced to share my pizza with the rest of the marketing team – and my pizza ain’t for sharing. There was no reason for Domino’s to be targeting me, and no reason for my work email to be on their systems.
None of the links took me to the Domino’s website
This one’s the kicker. Again, our Phisher has been a smart one; they’ve created an email address which, to the untrained eye, looks legitimate: dominos@[redacted].com. Must be legitimate, right? I mean, Domino’s is right there in the title…right?
Almost, but not quite. Any mega-corporation worth its salt would have its own branded .com address. Why is this leading me to a domain other than dominos.co.uk? And who are these “Digital Notification” guys anyway? That’s what I asked myself before the next big alarm bell.
The digital notifications site has no Google presence and no site security
Never has knowing so little about a company taught me so much about them. Sure, I could log on to the sender’s website and have a jolly good rummage through their service offerings, but the evidence certifies this as a Very Bad Idea.
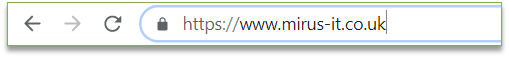
I did a quick Google search for the dodgy URL and found one very sorry-looking Google result. By hovering over the link, I could see that it redirected to an insecure connection unprotected by https.
For those not in the know, https is the secure version of http, the way our information used to be shared between two connections in a network. Any trustworthy URL will be noticeable simply by the addition of that extra ‘s’ – just check within your browser’s address bar. Many browsers also have the padlock icon seen here, confirming that the site you’re visiting is adequately secured.
In conclusion? This would be a solid phishing attempt if I weren’t so aware of the tell-tale signs, but it’s still scary how easy it could have been to click on one of many sketchy links, potentially exposing me to ransomware or data theft.
It’s likely that by clicking these links, users would soon be instructed to enter their Domino’s account details or, worse yet, their debit card info – all in exchange for a pizza dish they were never going to get. The phishers have smartly targeted a vast customer base too, and in doing so have a much better chance of hooking in a hapless victim.
So thanks, but no thanks, my pizza-flaunting fraudster. I might love the odd helping of anchovies, but I prefer my pizza completely phish-free.
Final Thoughts
(It was only a few weeks after writing this blog that I discovered these emails were part of a clandestine Phishing Awareness test at Mirus. While I successfully passed, I am yet to receive a pizza for my efforts!).
Would your workers recognise the tell-tale signs of a phishing attempt? Internal threats, including human error, are thought to be responsible for most data breaches in small to medium businesses.
Mirus’s Phishing and Security Awareness Services keep your people prepared for the threats of phishing attempts – get in touch to find out more, or arrange a free IT Security Assessment.


